FOXTROT/ALFA: Apple Doesn’t Encrypt iCloud to Please the FBI, Amazon Nations Upset of .amazon Sale to Amazon, The First Stable Version of Fedora CoreOS
Hi there! Welcome to FOXTROT/ALFA. This is issue 67 for Tuesday, 21 January 2020 and it’s another late one I am afraid. I was pretty busy today and had to finish a podcast on the shootdown of Ukraine International Airlines flight PS752 in Tehran before I could start compiling this letter. Let’s do this, though.
Online Crooks Selling “Temporary Social Security Numbers”
Spammers are currently trying to capitalise on widely publicised data breaches and the threat of identity theft that these bring to people whose data has been leaked. As Kaspersky reports, they are ripping off gullible internet users by trying to sell them “temporary social security numbers”.
Recently, a curious site caught our eye. Seemingly owned by a certain Personal Data Protection Fund, the website’s main page states that the fund was created by the “US Trading Commission.” A large banner at the top of the page announces that the fund awards compensation for leaks of personal data – for which citizens of any country in the world can apply. For those interested, the site offers to check whether your data has ever leaked. For this, you need to specify your surname, first name, phone number, and social media accounts. Above the input form is a warning that entering other people’s data will result in a severe penalty.
The charitable fund cannot send money without knowing your SSN (social security number), a nine-digit number issued to U.S. citizens as well as permanent and temporary working residents. But if you don’t have one, never fear: You can simply check the box next to the line “I’am don’t have SSN” (English grammar doesn’t seem to be the scammers’ strong point). To get around the problem of not having an SSN, the site offers to sell you a temporary one! In comparison with the amount of compensation dangling in front of your eyes, the $9 price tag is a trifle.
But what if you actually have a valid US social security number? Ha-ha!
If you do try to complete the transfer without buying an SSN, the site will return an error and demand a temporary number. And if by some chance you happen to specify a valid SSN in the fraudulent form, you will still be asked to buy a temporary one.
Those who decide to purchase a temporary SSN get redirected to a payment form. If you happen to do it from a Russian IP address, this payment form appears in Russian, and the purchase price is specified in rubles. This is strange. Why would a U.S. government agency require payment in a foreign currency?
Well, spoiler: This isn’t a US government site. Obviously.
Residents of other countries are likely to be redirected to a less suspicious English-language form asking for payment in dollars. Of course, this is scam. The Personal Data Protection Fund does not exist, and neither does the US Trading Commission, as you might have guessed.
What will these guys think of next?
South American Nations Upset Over .amazon Sale
ICANN has sold the .amazon TLD to Jeff Bezos’ giant tech company and eight South American countries (who border the river his bloody company was named for) are justifiably upset.
In a letter sent on Friday, the Amazon Cooperation Treaty Organization (ACTO) responded badly to a missive from ICANN’s president saying it was going ahead with adding the address to the global internet. Calling the decision “illegal and unjust,” as well as an “act of force,” it criticizes ICANN’s “attempts to legitimize a decision that was not taken under legitimate circumstances nor for legitimate reasons,” and vows vague revenge by “disseminating news of this situation to all relevant groups.”
The whole thing is a lot more complicated, though, as the whole saga has been ongoing for eight years. The Register has the whole story. If you don’t want to read it all, here’s the conclusion they draw:
ICANN continues to convince itself that it did the right thing, despite the evidence otherwise. There is no sign that the organization intends to carry out an After Action Review to highlight failings and make recommendations – a common approach in most large organizations but one which ICANN has never engaged in, leading it to repeat the same mistakes over and over again. ACTO is still furious – at least on paper – and government representatives have learnt they can delay ICANN processes for years by sending the occasional letter and giving the occasional speech. In the end, it still took the intervention of the US government to get the ball rolling.
And all the companies of the world have learnt, again, that when it comes to ICANN, its processes are unreliable and can at any point be overturned by arbitrary decisions made by unaccountable staff. Forcing the DNS overseer to follow its own rules will require years of effort and millions of dollars in lawyers’ fees. Given other controversies surrounding ICANN in recent months, including extracting $20m from Verisign to sign the dot-com extension agreement, and the furore over the proposed sale of .org to an unknown private equity firm, it is no wonder that calls for reform of ICANN have grown louder in recent days.
Apple isn’t Encrypting Its iCloud Backups Because The FBI Asked Nicely
Apple consistently paints itself as a company that cares about its users’ privacy, unlike those evil guys from Google and Microsoft. Guess what? It’s all PR. I’ve said so for years and it has, once again, become blatantly obvious. As Reuters now reports, Apple dropped plans to encrypt iCloud backups because the FBI complained.
Apple Inc dropped plans to let iPhone users fully encrypt backups of their devices in the company’s iCloud service after the FBI complained that the move would harm investigations, six sources familiar with the matter told Reuters. The tech giant’s reversal, about two years ago, has not previously been reported. It shows how much Apple has been willing to help U.S. law enforcement and intelligence agencies, despite taking a harder line in high-profile legal disputes with the government and casting itself as a defender of its customers’ information.
An Apple spokesman declined to comment on the company’s handling of the encryption issue or any discussions it has had with the FBI. The FBI did not respond to requests for comment on any discussions with Apple.
Guess what? Big companies don’t actually care about you. They care about their bottom line, which is directly affected by government regulations.
More than two years ago, Apple told the FBI that it planned to offer users end-to-end encryption when storing their phone data on iCloud, according to one current and three former FBI officials and one current and one former Apple employee. Under that plan, primarily designed to thwart hackers, Apple would no longer have a key to unlock the encrypted data, meaning it would not be able to turn material over to authorities in a readable form even under court order.
In private talks with Apple soon after, representatives of the FBI’s cyber crime agents and its operational technology division objected to the plan, arguing it would deny them the most effective means for gaining evidence against iPhone-using suspects, the government sources said. When Apple spoke privately to the FBI about its work on phone security the following year, the end-to-end encryption plan had been dropped, according to the six sources.
Reuters could not determine why exactly Apple dropped the plan. “Legal killed it, for reasons you can imagine,” another former Apple employee said he was told, without any specific mention of why the plan was dropped or if the FBI was a factor in the decision. That person told Reuters the company did not want to risk being attacked by public officials for protecting criminals, sued for moving previously accessible data out of reach of government agencies or used as an excuse for new legislation against encryption.
“They decided they weren’t going to poke the bear anymore,” the person said, referring to Apple’s court battle with the FBI in 2016 over access to an iPhone used by one of the suspects in a mass shooting in San Bernardino, California. Two of the former FBI officials, who were not present in talks with Apple, told Reuters it appeared that the FBI’s arguments that the backups provided vital evidence in thousands of cases had prevailed. “It’s because Apple was convinced,” said one. “Outside of that public spat over San Bernardino, Apple gets along with the federal government.”
Apple isn’t special. It’s a phone maker, like all the others. And fundamentally, it doesn’t matter what government weakens encryption – the one in China, the one in the US or my government here in Germany – the end result is the same. Someone please clue my colleagues in the mainstream media in on this, as they keep reporting that Huawei is evil and that Apple is the white knight fighting for all of our privacy. It’s laughable.
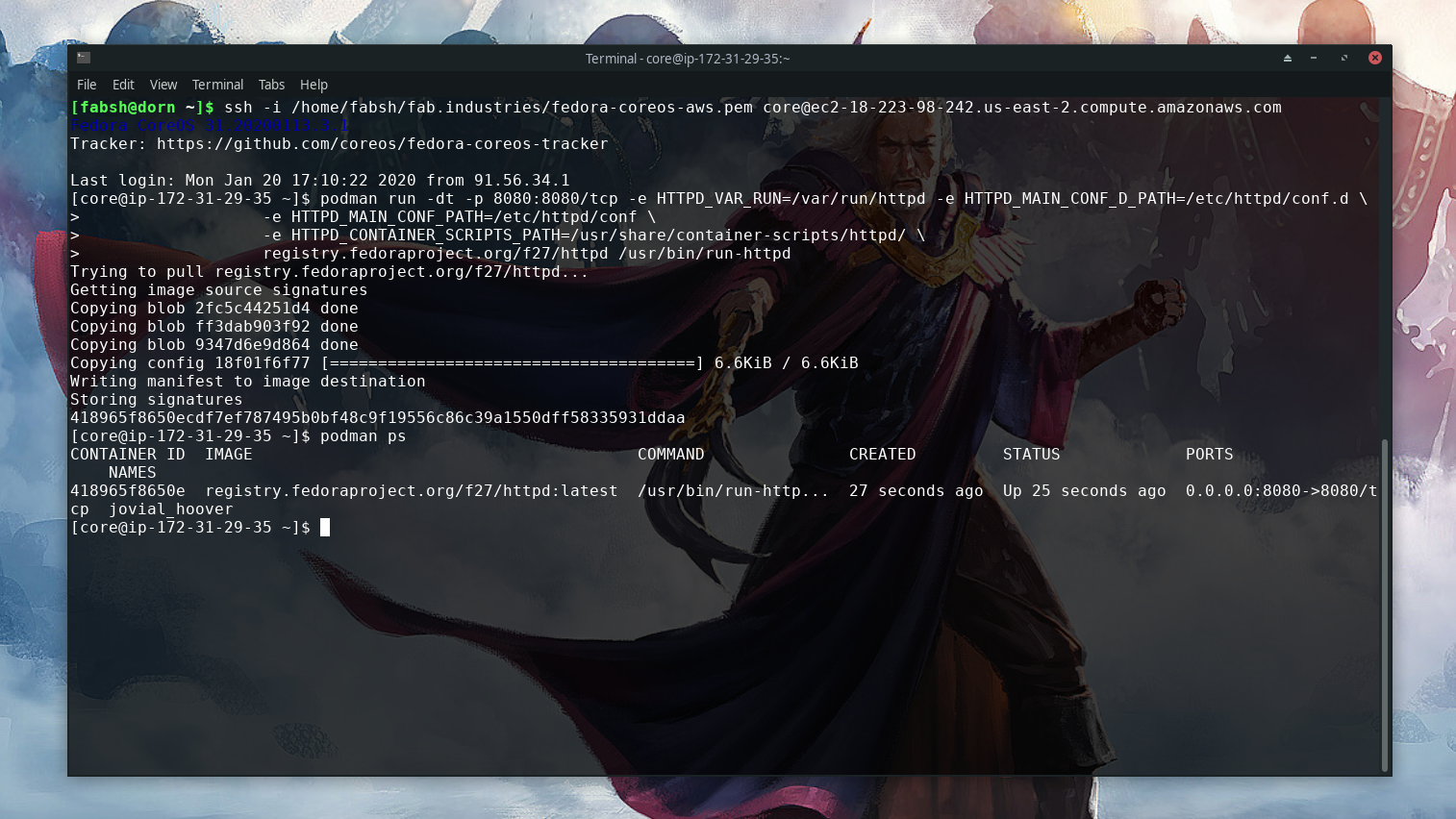
The First Stable Version of Fedora CoreOS is Here
The Fedora developers have released the first stable version of their new container distro Fedora CoreOS. I’ve tried it out on AWS and wrote the experience up on Heise  . This actually looks like it could be going somewhere, even if the documentation is a bit sparse at the moment. But containers and container orchestration are definitely Red Hat’s big focus at the moment.
. This actually looks like it could be going somewhere, even if the documentation is a bit sparse at the moment. But containers and container orchestration are definitely Red Hat’s big focus at the moment.
Attackers Might Soon Turn Windows’ Encryption Against Itself
The Encrypting File System (EFS) technology that’s part of NTFS, the file system used in modern Windows versions, can be used for the purposes of ransomware attacks.
The encryption technology Microsoft uses to protect Windows file systems can be exploited by ransomware. So says the research team at Safebreach Labs, which has demonstrated how file-scrambling software nasties can not only tap into the Windows Encrypting File System but also avoid anti-malware tools.
Safebreach veep of research Amit Klein and his team crafted proof-of-concept code that uses EFS to force a PC to encrypt its own data using an attacker-supplied key. The key is then flushed from the computer’s memory, leaving miscreants with the sole means for decrypting a victim’s information. The benefit of this, explained Klein, is an infection that is not only hard to spot and block, but can also be more easily automated, and executed without administrator clearance.
Also Noteworthy
Some other stories you might want to peruse, if you have some reading time:
- Looks like the party’s over, folks: Global PC sales set to shrink as Windows 10 upgrade cycle tails off, says Gartner
- How a Kaggle Grandmaster cheated in $25,000 AI contest with hidden code – and was fired from dream SV job
- Remember that Sonos speaker you bought a few years back that works perfectly? It’s about to be screwed for… reasons
- “I am done with open source”: Developer of Rust Actix web framework quits, appoints new maintainer
